If you need to troubleshoot configuring your Honeycomb Environments and Teams, explore these solutions to common issues.
Troubleshoot issues related to managing Environments.
Check that you have typed in the correct unique identifier of the environment you want to delete. It should be listed in parentheses in the prompt for the field.
Troubleshoot issues related to API Keys.
For security reasons, the full, 64-character API key is only available when you first create the API key. Only the non-sensitive first 32 characters of the API Key (a region-specific prefix and the key’s identifier) are available in the Honeycomb UI thereafter.
If you have misplaced the full API key, we recommend that you disable or delete the key, and create a new one.
Troubleshoot issues related to configuring access for Teams.
Troubleshoot team member authentication access that uses Google Single Sign-on (SSO).
When attempting to log in to Honeycomb using Google SSO, users may encounter a message stating that no accounts match their user credentials:
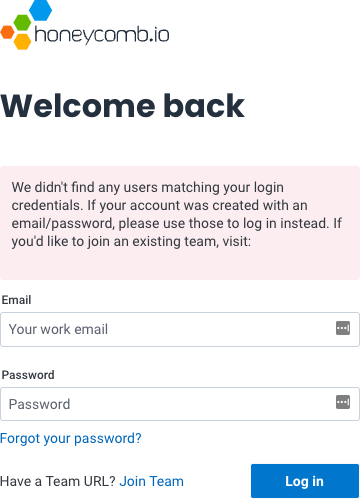
This message appears when the user’s team has configured Google SSO authentication and the user already has a Honeycomb account associated with email address/password as credentials.
To solve this issue, the user must link their Honeycomb account to their Google account.
After they have linked their Honeycomb and Google accounts, they can log in to Honeycomb using their Google account.
Troubleshoot team member authentication access that uses SAML Single Sign-on (SSO).
If a “SAML Assertion” error appears, verify that your SSO Identity Provider Audience and Recipient fields match your Honeycomb team settings SSO Service Provider Issuer/Entity ID and Service Provider ACS URL fields.
The Audience field should contain: https://ui.honeycomb.io/saml/<team-identifier>, while the Recipient field should contain: https://ui.honeycomb.io/auth/callback/saml/<team-identifier>.
Troubleshoot team member authentication access that uses Microsoft Entra ID Single Sign-on (SSO).
Honeycomb requires the FirstName, LastName, and Email claims to be populated.
If your Microsoft Entra accounts are configured to use a value other than user.givenname or user.surname to represent a user’s first or last name, you may use those other values to populate the corresponding claims instead.